Network Compliance Automation: Stop Checking Configs Manually
It’s Thursday afternoon. Your auditor just emailed. They want to see evidence that every Cisco IOS device in your PCI zone was compliant with your password policy on March 14th at 2:15 AM.
You have… a spreadsheet. Somewhere. From the last audit cycle. Updated manually by whoever was on shift. With a column for “reviewed” that’s mostly checkboxes. And a lot of yellow highlighting nobody remembers the meaning of.
You’ve got forty-eight hours.
If you work in enterprise networking, some version of this scene is your life. Network compliance automation isn’t a nice-to-have — it’s the only realistic way to keep pace with DISA STIG, CIS Benchmark, and PCI-DSS requirements across a modern multi-vendor environment. Yet the tools most teams use haven’t meaningfully changed since 2008: show running-config, Excel, a shared drive, and the prayer that nobody asks too many questions.
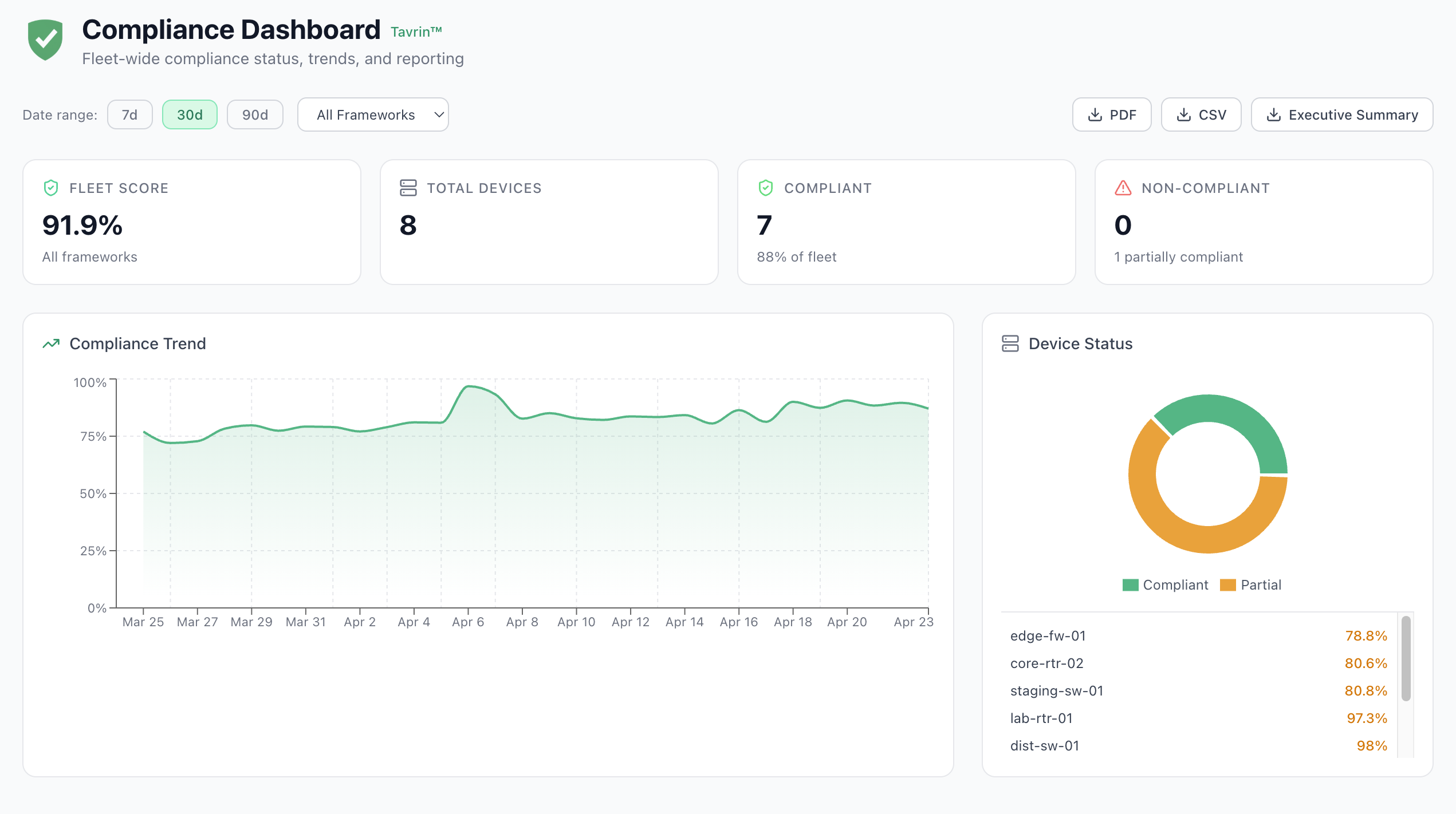
This is absurd. Network compliance should not be an annual fire drill. It should be a workflow that runs every night, produces tamper-proof evidence automatically, and lets any engineer — or any auditor — answer “was this device compliant at 2:15 AM on March 14th” in under thirty seconds.
That’s what modern network compliance automation looks like. Here’s what it takes to actually build it — and how we’re building it into Tavrin™.
The Spreadsheet Problem
Let’s be honest about why most enterprise networks are stuck in manual compliance land.
It’s not because tools don’t exist. Cisco ships compliance tooling. Juniper does. There are dozens of third-party network compliance products on the market. The problem isn’t availability — it’s that most of these tools solve one piece of the problem and demand you solve the rest yourself.
Common failure modes we hear from practitioners:
- Cloud-only tools ask you to upload device credentials to their SaaS. Security teams veto this on day one. Dead on arrival in regulated industries.
- Vendor-specific tools only check Cisco, or only check Juniper, or only check the vendor whose logo is on the box. Real networks have five vendors.
- “Agent-based” compliance tools require you to deploy an agent on every device — fine for servers, catastrophic for network gear.
- Standalone compliance silos don’t plug into your change-management, ticketing, or notification systems. So you get reports nobody reads.
- “Rule library” vendors sell you the rules as a subscription but require your team to author, edit, and maintain every profile. DISA STIG compliance alone is 2,000+ controls across five device families.
The net result: every network team eventually ends up maintaining some homegrown combination of Bash scripts, Python, an Excel template, and tribal knowledge. And that combination becomes brittle the moment someone leaves the team.
What Real Network Compliance Automation Looks Like
Before we talk about any specific tool — ours or anyone else’s — here’s the bar a modern network compliance automation system needs to clear:
Continuous, not quarterly. If your compliance posture is only checked during an audit cycle, drift is inevitable. Continuous means automated scans running nightly at minimum, ideally triggered by every change.
Multi-framework, single scan. A single Cisco IOS switch might need to pass CIS Benchmarks (your internal standard), PCI-DSS (regulatory), DISA STIG (if you’re federal-adjacent), and your company’s custom golden config. Running four separate audits is busywork. The engine should evaluate all of them in one pass.
Multi-vendor, natively. Cisco, Juniper, Arista, Palo Alto — whatever you run, the engine should speak it. Hierarchical Juniper configs aren’t just regex with extra steps.
Evidence-preserving. When the auditor asks about March 14th at 2:15 AM, the answer shouldn’t require rerunning a scan. Historical per-rule results should be immutable and queryable.
Composable, not standalone. Compliance results should feed directly into change-management workflows, ticketing, notifications, and remediation — not produce PDFs that nobody opens.
Credential-respecting. Secrets stay on your network. Full stop. The cloud should orchestrate, not hold keys to your kingdom.
That’s a tall order. Most tools meet two or three of these. Very few meet all six.
Introducing Tavrin™
Tavrin™ is the compliance engine built into Regnor™, our network automation platform. It was designed from day one to meet every item on that list.
Here’s how it works, in plain terms.
Compliance is a workflow node, not a silo
In Tavrin™, compliance isn’t a separate product hanging off the side. It’s a first-class workflow node you drop into any automation. Here’s what that looks like in the Regnor™ visual workflow designer:
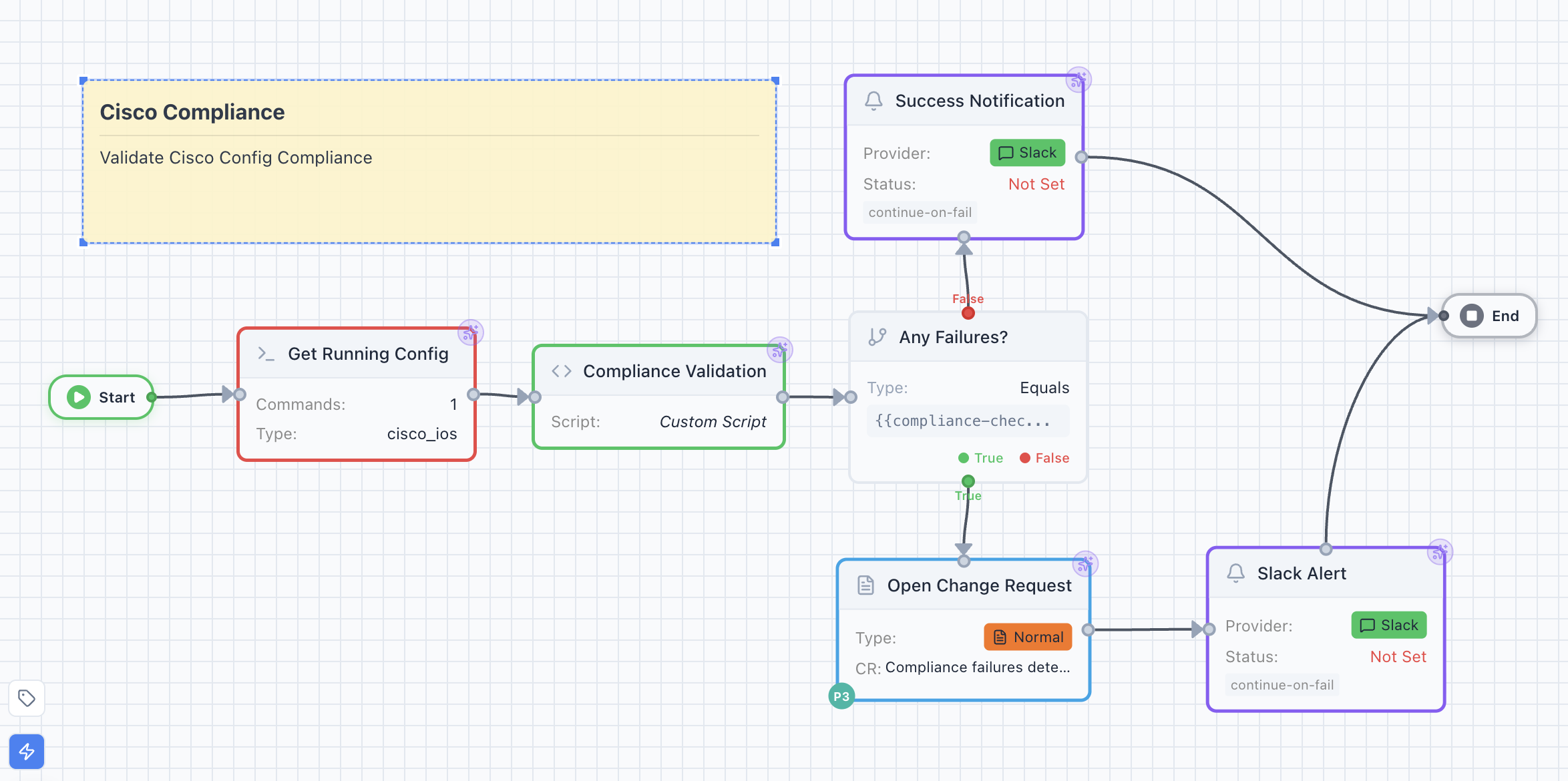
The compliance node consumes device configuration from an upstream node and evaluates it against one or more compliance profiles. Because it’s composable, you can chain it with:
- ITSM integrations — auto-open ServiceNow change requests for critical failures
- Notification nodes — ping Slack, email, or PagerDuty based on severity
- Conditional logic — branch on pass/fail, trigger remediation workflows
- Approval gates — require human sign-off before auto-remediation runs
- Pre-production testing — run the same compliance profile against a ContainerLab replica before deploying changes
Most compliance tools force you into their workflow. Tavrin™ becomes part of yours.
Batteries-included rule libraries
Tavrin™ ships with over 7,000 lines of curated compliance rules covering:
- CIS Cisco IOS Benchmarks (Levels 1 and 2)
- CIS Arista EOS Benchmarks
- DISA STIG — Cisco IOS (full CAT I/II/III severity mapping)
- DISA STIG — Juniper SRX (NDM, ALG, VPN, IDPS)
- DISA STIG — Juniper EX Switch (NDM, L2S, RTR)
- PCI-DSS Network Controls
- NIST 800-53 Network Controls
- SOX IT General Controls
- Basic Security Hardening (a sensible default for teams starting from zero)
You turn on Tavrin™ and you already have coverage. You don’t need to author a single rule. You don’t need a consulting engagement. And when new STIG versions ship, we update the profiles — not you.
On top of that, you can author your own “golden config” profiles for internal standards, and Tavrin™ will evaluate them side-by-side with the shipped templates.
Seven rule types, including hierarchical parsing
Under the hood, Tavrin™ supports seven rule types that let you express what you actually care about:
must_contain— line or substring matching (the basic case)must_not_contain— the inverse, with detailed violation reportingregex_match— regex matching with ReDoS-safe timeouts (more on that below)section_match— multi-line contiguous block matchingvalue_range— extract a value via regex and check it’s in an expected numeric rangehierarchical_match— full parse-tree evaluation for Juniper and nested Cisco configsmanual_review— a placeholder for STIG operational controls that require human judgment
That last one is important: honest compliance tools admit some controls can’t be machine-evaluated. Instead of pretending to pass them automatically, Tavrin™ flags them for human review and routes them into your workflow’s approval process.
The hierarchical rule type uses ciscoconfparse2 — the gold-standard open-source library for network config parsing — rather than regex hacks. When a Juniper SRX config says set security policies from-zone trust to-zone untrust, Tavrin™ understands the nested policy structure natively.
Severity-weighted scoring with custom thresholds
Not all failures are equal. A missing “banner login” is an informational finding. An unencrypted SNMP community string is a critical security failure.
Tavrin™ scores each device using a severity-weighted algorithm. The defaults:
| Severity | Weight |
|---|---|
| Critical | 10 |
| High | 5 |
| Medium | 2 |
| Low | 1 |
| Info | 0 |
A device with one critical failure can score lower than a device with twenty informational findings — exactly the way a human auditor would rank them.
Scores feed into four threshold policies:
- Strict — any critical failure is instant non-compliance
- Weighted — must score above a configurable threshold (default 80%)
- Lenient — at least half of actionable rules must pass
- Custom — you write a boolean expression like
critical_failures == 0 and score >= 90
That custom expression evaluator is one of Tavrin™’s quiet killer features. It’s a sandboxed Python AST evaluator that accepts comparisons, boolean operators, and a whitelisted set of result variables — nothing else. No eval(), no imports, no attribute access. You get expressive threshold logic without opening a code-injection hole.
The Evidence Problem (and Why Architecture Matters)
Here’s where most compliance tools fall apart. Scoring is the easy part. The hard part is producing evidence an auditor will accept.
Let me walk through three things Tavrin™ does that matter.
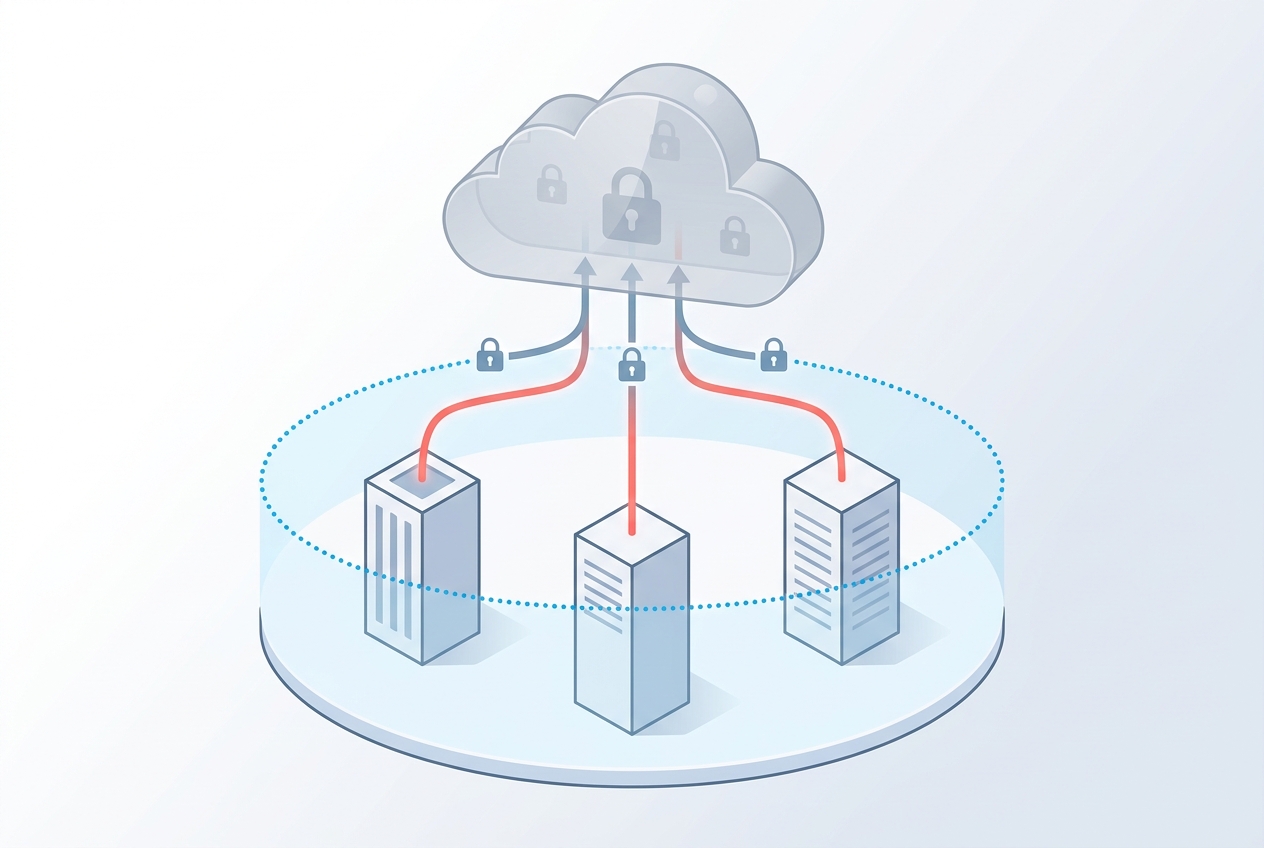
1. Credentials never leave your network
Regnor™ is a hybrid cloud-to-on-premise platform. Cloud handles workflow design, visualization, user management, and reporting. On-premise agents handle execution.
When a compliance scan runs:
- The cloud resolves which profiles apply to which devices (a join against device metadata)
- It sends the rule definitions to the on-premise agent along with the workflow
- The agent evaluates everything locally, inside your network
- The agent returns only the results — pass/fail counts and per-rule verdicts
The cloud sees: profile UUIDs, execution IDs, and structured compliance results. It does not see: device IP addresses, device credentials, or raw running configurations. Your secrets live in a local HashiCorp Vault alongside the agent. The cloud holds metadata about where to find them, never the secrets themselves.
For regulated industries — finance, healthcare, federal, critical infrastructure — this is non-negotiable. And it’s the default architecture, not a premium tier.
2. Evidence is immutable
Every compliance scan writes a record to a compliance_results table with:
- The execution ID, device, and profile it evaluated
- The full pass/fail/warn/skip/error breakdown
- Framework tags (so you can filter by “show me all my PCI evidence”)
- A JSONB blob containing every rule’s individual verdict — full context, not just counts
- A cryptographically signed timestamp
That last point matters: the results_json column stores the complete per-rule evidence for every execution. Drift analysis, auditor queries, and forensic reviews never need to re-run a scan — the historical evidence is archival.
And the database itself blocks tampering: an immutability trigger on the audit trail rejects any UPDATE or DELETE against past compliance records. You literally cannot rewrite history.
When the auditor asks “was router-37 compliant with CIS Level 1 at 02:15 UTC on March 14th?”, you hand them a single query result. They’re delighted. You’re done in thirty seconds instead of three days.
3. One device, many frameworks, one scan
Tavrin™ auto-matches profiles to devices based on vendor, OS, and tags. A single Cisco IOS switch in your “pci-zone” tag might automatically get evaluated against:
- CIS Cisco IOS L1 (your internal standard)
- PCI-DSS Network Controls (your regulatory baseline)
- DISA STIG Cisco IOS (because you have federal contracts)
- Your custom corporate golden config (because every company has one)
All in a single scan. All returning in a single workflow execution. All rolled up into one device score — and also available broken out by framework if the auditor wants to see PCI evidence specifically.
The alternative — running four separate scans with four separate tools and manually cross-referencing the results — is what most teams actually do today. It’s also what keeps compliance stuck in the “quarterly fire drill” model.
What This Unlocks
Once compliance is a workflow node instead of a standalone product, interesting patterns emerge.
Continuous compliance with Git-style change management. Every network change gets tested against compliance before it ships. Push a config update → pre-prod ContainerLab replica spins up → Tavrin™ validates → if clean, workflow proceeds. If not, the change is rejected with the specific rule that failed.
Automatic ticketing with full context. Critical failures chain into ServiceNow nodes that open change requests with the failing rule text, the offending config lines, and the recommended remediation — all populated via Jinja2 templates. Your NetOps team gets actionable tickets, not alert noise.
Multi-channel alerting, routed by severity. Critical failures ping PagerDuty. High-severity failures go to Slack. Informational findings roll up into a weekly email summary. All via nodes you wire up once and reuse forever.
Executive reports on demand. Need a PDF for the CISO’s Tuesday meeting? Tavrin™ exports executive summaries with STIG scorecards, top-five risks, CAT I highlights, and trend data — generated on-demand from preserved evidence, no rescan required.
Federal-ready from day one. CAT I/II/III severity badges, Vuln ID tracking on CSV exports, DISA STIG profiles out of the box. If your sales pipeline includes federal contracts, Tavrin™ doesn’t add six months to your compliance timeline.
What’s Next
We’re honest about what ships and what doesn’t:
- Drift-timeline visualization — the data is preserved; the dedicated timeline UI is in active development
- Expanded remediation library — today’s auto-remediation is Netmiko-based and opt-in; NAPALM and Scrapli remediation come next
- First-party SIEM connectors — for now, the
audit_trailtable is your SIEM integration point; dedicated Splunk/Elastic connectors are on the roadmap
What’s shipping today is enough to replace the spreadsheet forever. What’s coming next makes the whole thing disappear into your existing ops workflow.
Frequently Asked Questions
What is network compliance automation?
Network compliance automation is the practice of continuously evaluating network device configurations against security baselines (CIS Benchmarks, DISA STIG, PCI-DSS, NIST 800-53, or custom golden configs) using software instead of manual audits. A modern compliance automation system pulls configurations from devices, evaluates them against a rule library, scores the results, and stores immutable evidence for audit and drift analysis.
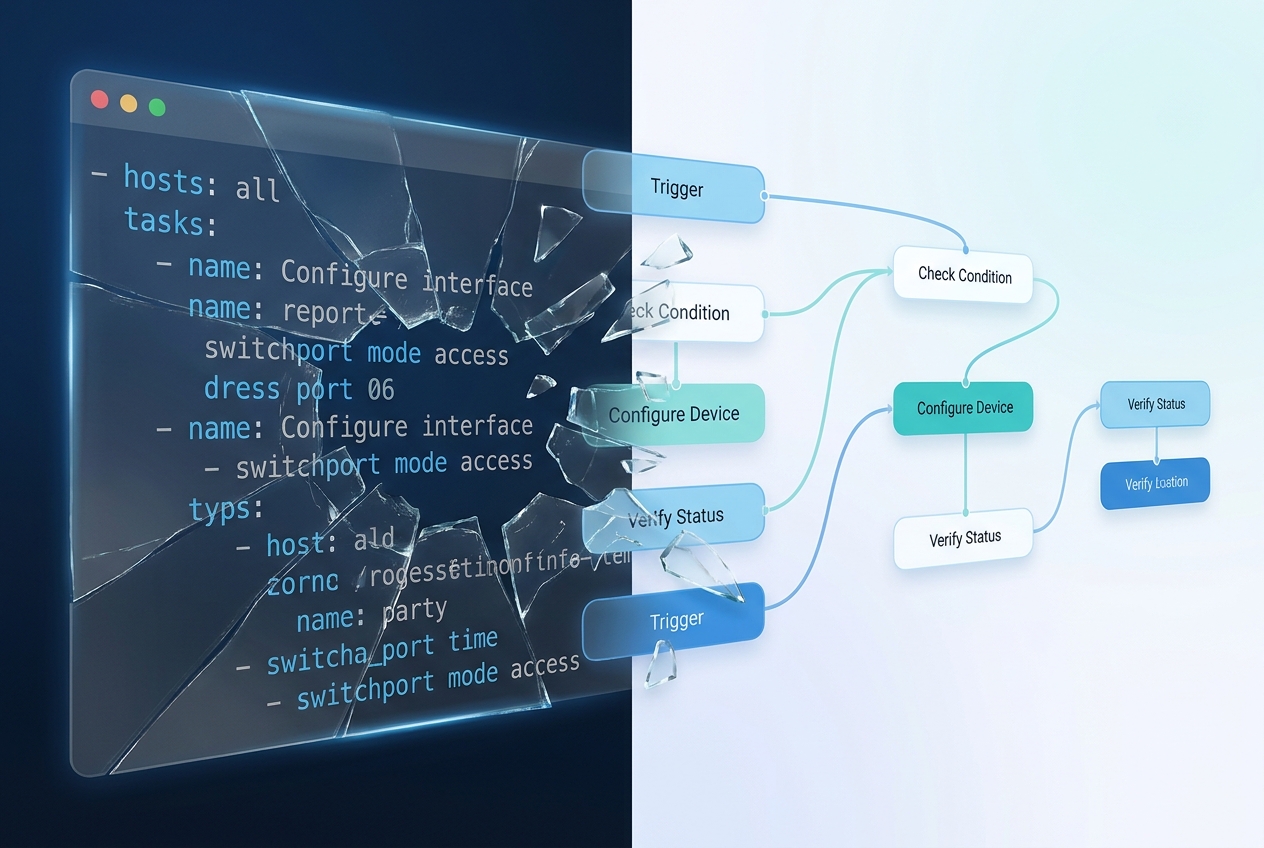
How is this different from Ansible or Python scripts?
Ansible playbooks and custom Python scripts can check compliance, but they don’t typically preserve immutable evidence, produce auditor-ready reports, support multiple frameworks in a single scan, or integrate natively with ticketing and notification systems. Purpose-built network compliance automation platforms handle evidence preservation, severity-weighted scoring, multi-framework evaluation, and composable workflows out of the box.
Does network compliance automation work with multi-vendor environments?
Yes — good compliance automation platforms evaluate configurations from Cisco, Juniper, Arista, Palo Alto, and other vendors in a single workflow. Tavrin™ ships with 7,000+ lines of rules covering CIS Cisco IOS, CIS Arista EOS, DISA STIG for Cisco IOS and Juniper SRX / EX platforms, plus generic PCI-DSS / NIST / SOX controls that work across vendors.
How do I handle compliance without exposing device credentials to the cloud?
Use a hybrid architecture where cloud components handle workflow design and reporting, while on-premise agents handle device connections and rule evaluation. With this model, device credentials, IP addresses, and raw configurations never leave your network — the cloud only sees structured compliance results. This is how Regnor™ is designed by default, not as an optional tier.
Can compliance automation replace my annual audit?
It can replace the spreadsheet-driven evidence gathering that makes audits painful. Auditors still need to sign off, but continuous compliance automation means you walk into every audit with immutable historical evidence, per-rule verdicts, and executive summary reports ready to hand over — reducing audit prep from weeks to hours.
Stop Checking Configs Manually
If you spent last month’s audit cycle manually diffing running configs against a baseline document, you already know the pain. You don’t need to keep living it.
Network compliance automation isn’t a luxury — it’s table stakes for any network team operating at enterprise scale. And the right architecture matters: on-premise evaluation, immutable evidence, multi-framework scoring, and composable workflows aren’t optional features. They’re what separates tools that get deployed from tools that get demoed.
Related reading on AutomateNetOps.AI:
- How AI is Changing Network Troubleshooting in 2026 — the AI story behind Regnor™
- Zero-Trust Credentials Security: Why Your Automation Secrets Should Never Leave Your Network — the architecture behind Claim #1 above
- Why On-Premise Matters for Network Automation Security — the full on-prem argument
Tavrin™ and Regnor™ are in beta today. If this sounds like the audit workflow your team deserves, we’d love to show you.
Tags: automation, cis-benchmarks, compliance, disa-stig, network-security, regnor, tavrin
Categories: Compliance, Network Automation
Updated:
You may also enjoy
How Regnor™ synchronizes credentials across multi-agent on-premise deployments without ever exposing plaintext to the cloud control plane — and how HMAC comm...
In November 2025, Ansible release 12 shipped with a quiet, catastrophic bug: the network device configuration modules stopped accepting Jinja2 templates as i...